Why Your Asset Inventory Determines Your Security Posture (And How Most Teams Get It Wrong)


You just got an alert about a critical vulnerability. CVSS 9.8. Sounds urgent, right?
But here's the question that actually matters: Is that vulnerability on an internet-facing production server handling customer data, or is it on an air-gapped test machine that gets rebuilt every week?
If you can't answer that question in seconds, you have an asset inventory problem. And that problem is affecting every security decision you make.
The Foundation Everyone Overlooks
Most security teams focus on the exciting parts: threat hunting, incident response, zero-trust architectures. Asset inventory sounds like IT housekeeping by comparison.
Here's the reality: You can have the best vulnerability scanners, the most advanced threat intelligence, and a talented security team. If you don't know what assets you have, where they are, and what they're worth to your business, you're making decisions in the dark.
The industry recognizes this. CIS Control #1 isn't about firewalls or encryption or detection. It's about knowing what you have. CISA includes comprehensive asset inventory as a foundational Cybersecurity Performance Goal. There's a reason it comes first.
The Unmanaged Asset Problem
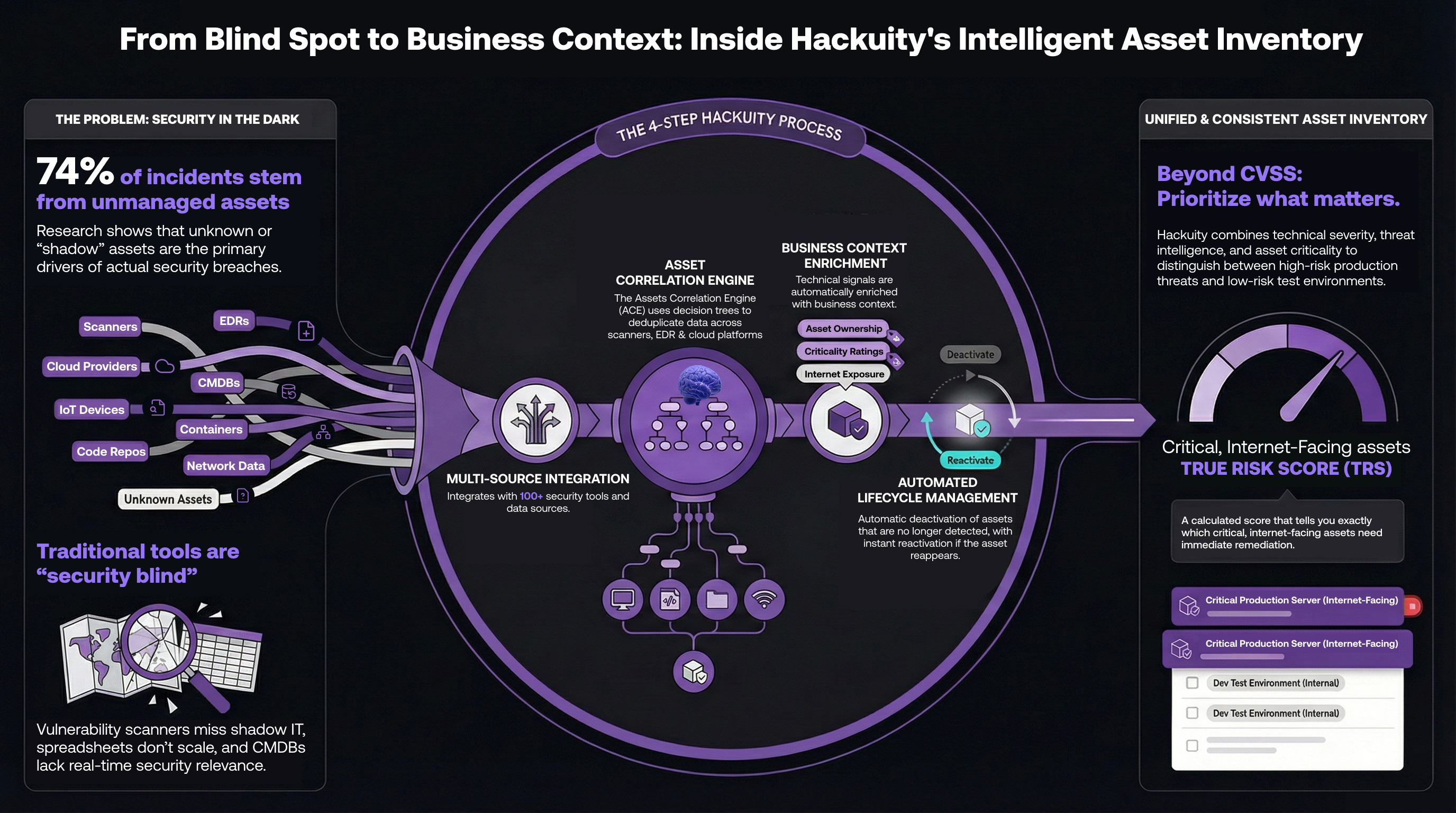
Research published in 2025 quantified what many security teams already suspected: 74% of organizations have experienced security incidents specifically due to unknown or unmanaged assets1. Not theoretical risk. Actual incidents.
The same research found that despite 91% of security leaders acknowledging that attack surface management directly impacts business risk, only 43% use dedicated tools to manage it proactively. Over half have no continuous processes in place at all.
When a critical vulnerability or breach hits, organizations scramble to answer basic questions: Where is this software deployed? Which systems are affected? How critical are those systems? Without accurate asset inventory, incident response becomes guesswork.
So why is this still a problem? Because traditional approaches weren't designed for what modern security actually needs.
Why Traditional Approaches Fall Short
Most organizations try one of three approaches. Each has real limitations.
The Single-Source Approach relies on your vulnerability scanner's asset inventory. Problem: It only sees what it can scan. Shadow IT? Invisible. Cloud-native services? Misses most of them. That unmanaged asset causing your next incident? Not on the list.
The Spreadsheet Approach exports data from multiple tools for manual deduplication. Problem: Doesn't scale. By the time you've finished deduplicating this week's data, your environment has changed. Good luck maintaining business context (ownership, criticality, exposure) across thousands of assets in Excel.
The CMDB Approach uses your IT service management CMDB as truth. Problem: CMDBs track purchased assets, not security-relevant reality. Shadow IT, developer-provisioned cloud infrastructure, containers that live for seconds? Not in your CMDB.
The fundamental issue: None of these were designed for what vulnerability operation centers actually need. Real-time, comprehensive visibility across all asset types, with business context attached, automatically deduplicated across dozens of data sources.
That's a different problem. It requires a different solution.
Why Intelligent Correlation Matters
The challenge isn't collecting asset data. Modern security tools generate plenty. The challenge is making sense of conflicting, duplicated, incomplete data from dozens of sources.
Think about what happens when you integrate multiple tools:
- Tenable reports an asset with an IP and FQDN
- Tanium reports a hostname, MAC address, a technical agent identifier
- CrowdStrike reports an endpoint with its own agent identifier
- Your cloud platform reports a VM with instance ID and tags
- Are these four different assets? Or one asset seen by four tools?
Simple matching won't cut it. You need logic that understands identifier trustworthiness. Agent IDs are highly reliable. MAC addresses are solid. FQDNs are good. IP addresses alone are problematic, especially with DHCP, NAT, or containers that exist for seconds.
Different asset types need different logic. Correlating physical servers isn't the same as correlating web applications. Or container images. Or cloud entities.
And you need to do this automatically, at scale, every time new data arrives. Manual correlation doesn't work when you're managing tens of thousands of assets.
Hackuity's Intelligent Asset Inventory (ACE).
We built Hackuity around a simple observation: Vulnerability Operation Centers don't need another asset inventory tool. They need an intelligence layer that makes sense of all the asset data they already have.
That's why we built the Assets Correlation Engine (ACE).
ACE uses decision tree logic to determine whether incoming data represents a new asset or additional information about an existing one. It handles six distinct asset categories: HOST, APP, CODE, CONTAINER_IMAGE, ENTITY, and WIFI. Each category requires different correlation logic optimized for how security tools actually identify them.
Multi-source integration means you don't choose between tools. We connect to 100+ security platforms and aggregate data from everything you already use. Your vulnerability scanners, EDR platforms, cloud security tools, EASMs and CMDBs all feed into a unified view.
Asset enrichment adds the business context technical scans can't provide: ownership, criticality ratings, exposure classifications, custom fields. This is what transforms technical asset data into risk-based prioritization.
Lifecycle management keeps inventory current automatically. Assets not seen for a configurable period get deactivated. Deactivated assets can be deleted after another period. If a deactivated asset appears again in any scan, it gets reactivated automatically.
With accurate, contextualized asset inventory in place, our True Risk Score (TRS) combines vulnerability severity with threat intelligence and asset context to calculate actual risk in your environment.
That CVSS 8.2 vulnerability we talked about? TRS distinguishes between the one on your internet-facing critical server (fix immediately) and the one on your air-gapped test system (accept risk). Same vulnerability severity. Radically different risk.
What This Changes
Asset inventory isn't sexy. It's foundational work.
But here's what matters: Everything else depends on it.
You can't do risk-based vulnerability management without knowing which assets are critical and exposed. You can't detect coverage gaps without knowing what assets exist. You can't route findings to the right owners without asset ownership data. You can't measure risk reduction without baseline asset context.
Every mature security capability you're trying to build sits on top of asset inventory. Get it wrong, and everything else gets harder. Get it right, and everything else becomes possible.
When that next critical vulnerability alert arrives, you'll know exactly what you're dealing with and what it means.
That's not just better asset management. That's better security.
Footnotes
Trend Micro (2025). "New Research Reveals Three Quarters of Cybersecurity Incidents Occur Due to Unmanaged Assets." Global study of 2,000+ cybersecurity leaders across 21 countries. Source ↩