Is Claude the new scanner?

For two decades, cybersecurity teams have relied on a familiar arsenal: SAST scanners, DAST scanners, infrastructure scanners, CNAPPs, EDR telemetry, and endless streams of CVEs. Detection logic evolved.
Coverage expanded. Dashboards multiplied. But the operating model itself barely changed.
Then came generative AI.
And suddenly, the question is no longer whether AI can assist security scanners.
The question is whether AI models like Anthropic’s Claude are becoming scanners themselves.
Fact #1: The Scanner Revolution Has Already Started
Most people still think about AI in cybersecurity as a copilot for analysts, a smarter chatbot, or an assistant helping developers write code faster.
That view is already outdated.
Claude has demonstrated something fundamentally different: the ability to reason about vulnerabilities, understand complex codebases, chain attack paths together, identify insecure logic, and even emulate offensive security behaviors with minimal supervision.
Projects like Mythos push this even further.
The industry is now entering a phase where AI is no longer simply augmenting traditional detection engines. AI is increasingly acting as the detection engine.
That changes everything.
Traditional scanners operate on deterministic logic:
- signatures
- rules
- pattern matching
- heuristics predefined
- vulnerability classes
Claude operates differently.
It reasons. It correlates context.
It understands intent.
It identifies insecure design patterns that were never explicitly programmed into a detection rule.
It can analyze relationships between components, business logic flaws, privilege boundaries, and trust assumptions in ways that classical scanners struggle to achieve.
Even without specialized frameworks like Mythos, Claude already exhibits capabilities that would have sounded absurd only a few years ago:
- identifying vulnerable code paths
- generating exploit hypotheses
- discovering insecure configurations
- understanding authentication flows
- analyzing infrastructure-as-code
- reviewing CI/CD pipelines
The implication is enormous.
The cost of vulnerability discovery is collapsing. And when the cost of discovery collapses, the volume explodes.
The cybersecurity industry has spent years preparing for more attackers. It is not prepared for an industrialization of vulnerability discovery itself.
We are rapidly approaching a world where discovering vulnerabilities becomes partially autonomous, massively scalable, and continuously accessible.
Not just for elite researchers.
For everyone.
Fact #2: AI-Driven Detection Is Accelerating the Rise of VulnOps
This avalanche of findings creates a new problem, detection is no longer the bottleneck but operations are.
This is precisely why VulnOps is emerging as a critical discipline inside modern enterprises.
VulnOps — Vulnerability Operations — is the operational framework designed to manage vulnerability remediation at scale. It combines detection, prioritization, orchestration, risk contextualization, ownership, remediation workflows, and executive visibility into a unified operational model.
Historically, vulnerability management programs were already struggling under the weight of traditional scanners.
Now imagine multiplying detection capacity by 10.
Or 100.
Or potentially far more.
That is the real disruption AI introduces.
The challenge is no longer: “Can we find vulnerabilities?”
The challenge becomes: “What do we do with millions of findings arriving continuously from dozens of AI-driven discovery systems?”
This is where AI simultaneously becomes both the problem and the solution because AI-powered discovery engines like Claude massively increase the number of findings entering the Vulnerability Operation Center (VOC).
As a result, organizations that continue operating vulnerability management programs with spreadsheet-era processes will not survive the incoming scale problem - The winners will be organizations capable of transforming vulnerability remediation into a continuous operational pipeline.
Fact #3: Claude Is Not Just a Code Scanner
When people first hear about Claude and vulnerability discovery, they instinctively think about secure code review, and that makes sense.
Large Language Models are naturally effective at:
- source code analysis
- insecure function detection
- dependency review
- application logic analysis
- API misuse detection
But limiting Claude to application security misses the bigger picture, Claude can also operate against infrastructure, systems, and live environments, we are now seeing the emergence of AI-assisted:
- host analysis
- configuration auditing
- Active Directory assessment
- cloud posture analysis
- automated penetration testing workflows
This is where things become truly disruptive, because traditional scanners typically remain constrained to predefined checks – but - Claude, however, can dynamically adapt its reasoning during an assessment.
It can:
- interpret the first outputs
- change strategy
- pivot laterally
- understand context
- emulate attacker thinking
That starts looking far less like scanning… and far more like autonomous offensive security operations, consequently, the line between scanner, pentester, analyst, and operator is beginning to blur.
And that may be the most important shift of all.
Fact #4: Hackuity Matters in an AI-Driven VulnOps World
The future will not consist of a single scanner; it will consist of hundreds of AI-powered discovery sources:
- AI code analyzers
- AI pentesting agents
- AI infrastructure assessment tools
- AI cloud security engines
- AI red teaming systems
Each generating enormous volumes of findings, raw detection alone has no value if organizations cannot operationalize the output. This is exactly where Hackuity changes the equation.
Hackuity acts as the operational backbone of modern VulnOps by aggregating assets and findings information from heterogeneous detection ecosystems — including AI-driven discovery systems powered by Claude and similar technologies.
The real innovation is not simply aggregation, but operational intelligence, Hackuity enables organizations to:
- centralize findings from multiple AI sources, normalize heterogeneous AI results and correlate duplicated vulnerabilities
- contextualize technical risk and prioritize remediation efforts
- orchestrate remediation workflows, accelerate vulnerability treatment and measure operational performance across the entire remediation lifecycle
In other words, AI increases discovery velocity, Hackuity enables organizations to survive it.
Fact #5: Hackuity is ready
Hackuity already supports multiple MCP interaction models, but let’s look at a real-world example: running SCA and SAST scans against the infamous application called “vulnerable-java-application”.
Step 1: Create Your SCA and SAST Skills in Claude
Not sure how to build them?
No problem — Hackuity can provide ready-to-use “Skills Library” examples to help you get started in minutes.
Step 2: Run the scan.
For example: /sast_sca_audit vulnerable-java-application`
That’s it.
Simple.
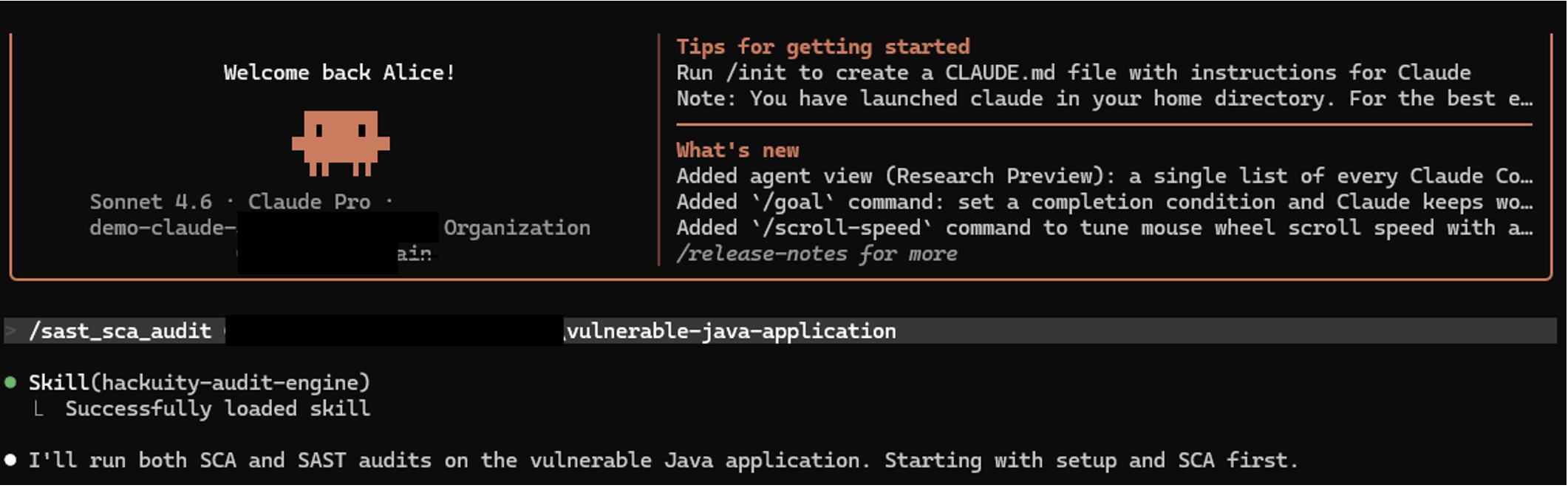
Step 3: Let’s begin the magic.



Simple.
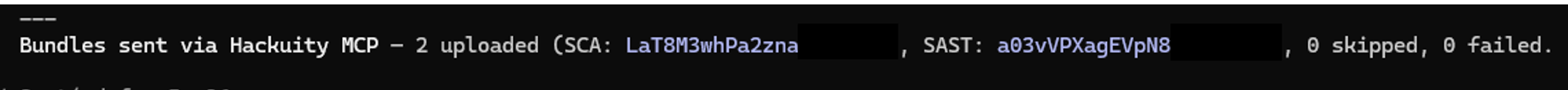
Step 4: Watch the Assessment Automatically Land in Hackuity
Once the analysis is completed, the assessment is automatically uploaded into through MCP or API integration.
No special workflow.
No custom processing.
No friction.
Your AI-powered vulnerability assessment simply becomes another fully operational component of the VulnOps pipeline:
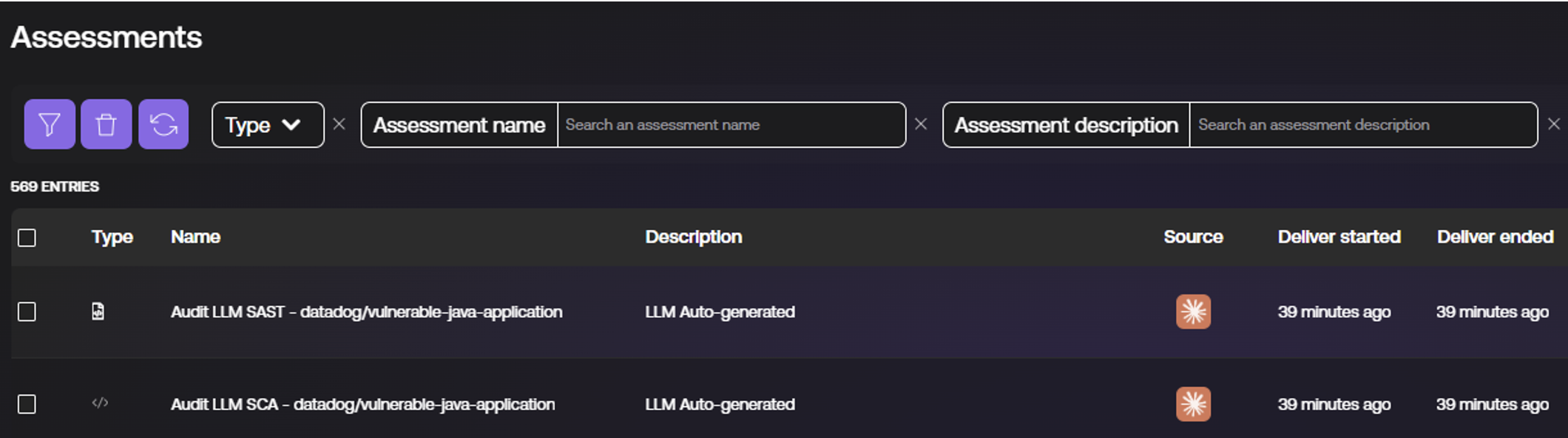
Step 5: Review the Asset Automatically Created in Hackuity
Because Claude was used to analyze source code, Hackuity automatically classifies the asset as a project repository.
No manual enrichment required.
The platform automatically adapts the asset context to the nature of the assessment.
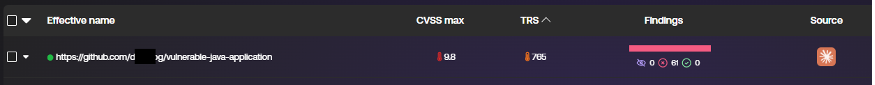
Step 6: Explore the Findings Generated by Claude
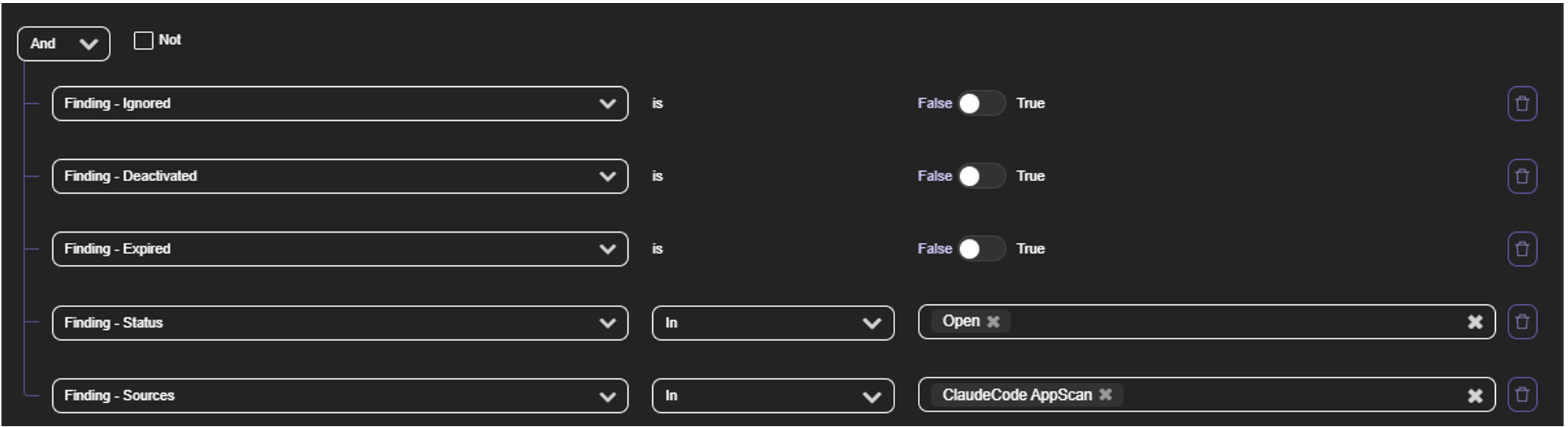
Hackuity then exposes the complete findings list produced by Claude.
Each finding includes:
- the full scan history generated by Claude
- detailed vulnerability information
- assessment traceability across executions
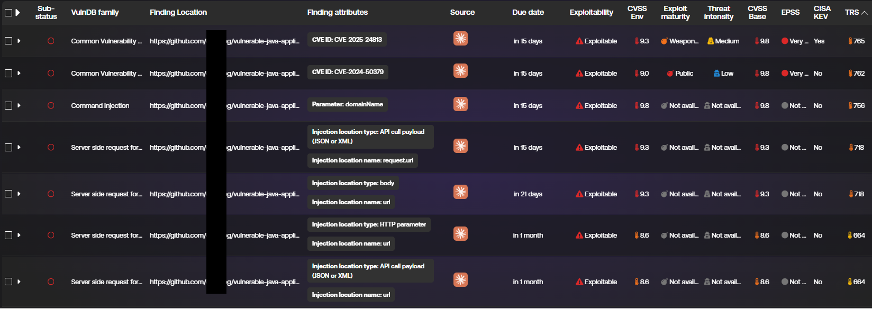
In other words, AI-generated findings are not isolated outputs anymore.
They become fully operationalized security intelligence inside the Hackuity Vulnerability Operation Center.
Takeaway
What we are witnessing is not simply the evolution of vulnerability scanning, but the emergence of a completely new cybersecurity operating model. AI systems like Claude are transforming vulnerability discovery into something faster, more contextual, and potentially continuous.
But as detection becomes industrialized, the real challenge shifts toward operations: prioritizing, orchestrating, and remediating at machine speed. This is precisely why VulnOps matters — and why platforms like Hackuity are becoming essential. The future of cybersecurity may no longer belong to the organizations that find the most vulnerabilities, but to those capable of operating them faster than everyone else.



